本文介绍如何配置ACK One GitOps多租户权限并进行权限验证。
索引
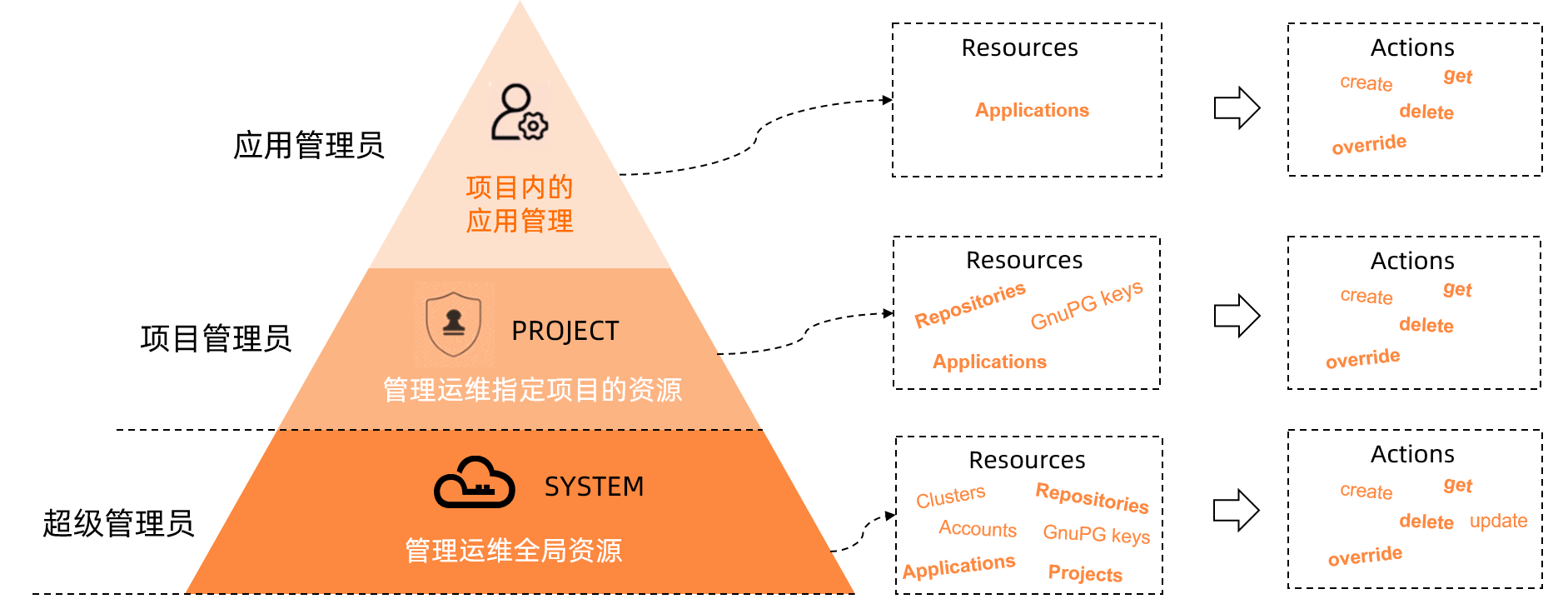
权限模型
使用场景
| 用户 | 角色 | 资源范围 | 权限 |
| admin | 超级管理员 | 所有 |
|
| team01-admin | 项目管理员 | Project team01 | 查询、新增、修改或删除Repositories等Project级别资源。 |
| team02-admin | 项目管理员 | Project team02 | 查询、新增、修改或删除Repositories等Project级别资源。 |
| team01-user01 | 应用管理员 | team01/production-app | 查询、新增、修改或删除team01/production-app应用。 |
| team01-user02 | 应用管理员 | team01/staging-app | 查询、新增、修改或删除team01/staging-app应用。 |
配置ACK One GitOps多租户权限
- 执行以下命令,编辑ArgoCD
argocd-cm的ConfigMap文件。kubectl edit cm argocd-cm -n argocd - 在
argocd-cm的ConfigMap文件中,新增本地用户。data: accounts.team01-admin: login accounts.team01-admin.enabled: "true" accounts.team01-user01: login accounts.team01-user01.enabled: "true" accounts.team01-user02: login accounts.team01-user02.enabled: "true" accounts.team02-admin: login accounts.team02-admin.enabled: "true" - 执行以下命令,编辑ArgoCD
argocd-rbac-cm的ConfigMap文件。kubectl edit cm argocd-rbac-cm -n argocd - 在
argocd-rbac-cm的ConfigMap文件中,新增如下内容为本地用户设置RBAC规则。展开查看本地用户的RBAC规则内容data: policy.csv: | ... p, role:team01-admin, projects, get, team01, allow p, role:team01-admin, repositories, *, team01/*, allow p, role:team01-admin, applications, *, team01/*, allow p, role:team01-admin, repositories, get, *, allow p, role:team01-admin, clusters, get, *, allow p, role:team02-admin, projects, get, team02, allow p, role:team02-admin, repositories, *, team02/*, allow p, role:team02-admin, applications, *, team02/*, allow p, role:team02-admin, repositories, get, *, allow p, role:team02-admin, clusters, get, *, allow p, role:team01-user01, projects, get, team01, allow p, role:team01-user01, repositories, get, team01/*, allow p, role:team01-user01, repositories, get, *, allow p, role:team01-user01, clusters, get, *, allow p, role:team01-user01, applications, *, team01/production-app, allow p, role:team01-user02, projects, get, team01, allow p, role:team01-user02, repositories, get, team01/*, allow p, role:team01-user02, repositories, get, *, allow p, role:team01-user02, clusters, get, *, allow p, role:team01-user02, applications, *, team01/staging-app, allow ... g, team01-admin, role:team01-admin g, team02-admin, role:team02-admin g, team01-user01, role:team01-user01 g, team01-user02, role:team01-user02 - 使用admin用户登录ArgoCD系统,查看本地用户并为其设置密码。
- 执行以下命令,查看本地用户。
预期输出:export ARGOCD_OPTS='--port-forward-namespace argocd --port-forward' argocd account listNAME ENABLED CAPABILITIES admin true apiKey, login team01-admin true login team01-user01 true login team01-user02 true login team02-admin true login - 执行以下命令,为本地用户设置密码。
argocd account update-password --account <username> --current-password <current password> --new-password <new password>
- 执行以下命令,查看本地用户。
- 使用admin用户登录ArgoCD系统,执行以下命令,添加全局Repositories。
argocd repo add https://code.aliyun.com/bigteam/echo-server01.git argocd repo add https://code.aliyun.com/bigteam/echo-server02.git argocd repo list TYPE NAME REPO INSECURE OCI LFS CREDS STATUS MESSAGE PROJECT git https://code.aliyun.com/bigteam/echo-server01.git false false false false Successful git https://code.aliyun.com/bigteam/echo-server02.git false false false false Successful - 使用admin用户登录ArgoCD系统,执行以下命令,创建和配置Project team01和Project team02。
类别 Git Repository Cluster 允许Project team01使用的资源 https://code.aliyun.com/bigteam/echo-server01.githttps://47.111.XX.XX:6443允许Project team02使用的资源 https://code.aliyun.com/bigteam/echo-server02.githttps://47.97.XX.XX:6443argocd proj create team01 argocd proj add-source team01 https://code.aliyun.com/bigteam/echo-server01.git argocd proj add-destination team01 https://47.111.XX.XX:6443 "*" argocd proj create team02 argocd proj add-source team02 https://code.aliyun.com/bigteam/echo-server02.git argocd proj add-destination team02 https://47.97.XX.XX:6443 "*" - 使用team01-admin用户和team02-admin用户,分别在Project内创建Repositories。
- 使用team01-admin用户操作
- 执行以下命令,使用team01-admin用户登录。
argocd login Username: team01-admin Password: 'team01-admin:login' logged in successfully Context 'port-forward' updated - 执行以下命令,在Project team01内创建Repositories。
预期输出:argocd repo add https://code.aliyun.com/team01/echo-server.git --project team01Repository 'https://code.aliyun.com/team01/echo-server.git' added
- 执行以下命令,使用team01-admin用户登录。
- 使用team02-admin用户操作
- 执行以下命令,使用team02-admin用户登录。
argocd login Username: team02-admin Password: 'team01-admin:login' logged in successfully Context 'port-forward' updated - 执行以下命令,在Project team02内创建Repositories。
预期输出:argocd repo add https://code.aliyun.com/team02/echo-server.git --project team02Repository 'https://code.aliyun.com/team02/echo-server.git' added
- 执行以下命令,使用team02-admin用户登录。
- 使用team01-admin用户操作
验证ACK One GitOps权限模型
测试项目管理员的资源操作权限
Projects资源操作
使用以下命令,测试team01-admin对Projects资源的操作权限。
argocd account can-i create projects "*"
no
argocd account can-i update projects "team01"
no
argocd account can-i delete projects "team01"
no
argocd account can-i get projects "team01"
yes
argocd account can-i get projects "team02"
no以上结果表明,项目管理员只能查看Project team01,无其他操作权限。
Repositories资源操作
使用以下命令,测试team01-admin对Repositories资源的操作权限。
argocd account can-i create repositories "*"
no
argocd account can-i update repositories "*"
no
argocd account can-i delete repositories "*"
no
argocd account can-i get repositories "*"
yes
argocd account can-i create repositories "team01/*"
yes
argocd account can-i update repositories "team01/*"
yes
argocd account can-i delete repositories "team01/*"
yes
argocd account can-i get repositories "team01/*"
yes以上结果表明,项目管理员只能查看全局Repositories和Project team01的Repositories资源查询、新增、修改或删除的权限。
Clusters资源操作
使用以下命令,测试team01-admin对Clusters资源的操作权限。
argocd account can-i create clusters "*"
no
argocd account can-i update clusters "*"
no
argocd account can-i delete clusters "*"
no
argocd account can-i get clusters "*"
yes
argocd account can-i create clusters "team01/*"
no
argocd account can-i update clusters "team01/*"
no
argocd account can-i delete clusters "team01/*"
no以上结果表明,项目管理员只能查看全局Clusters,无其他操作权限。
Applications资源操作
使用以下命令,测试team01-admin对Applications资源的操作权限。
argocd account can-i create applications "*"
no
argocd account can-i update applications "*"
no
argocd account can-i delete applications "*"
no
argocd account can-i get applications "*"
no
argocd account can-i create applications "team01/*"
yes
argocd account can-i update applications "team01/*"
yes
argocd account can-i delete applications "team01/*"
yes
argocd account can-i get applications "team01/*"
yes以上结果表明,项目管理员只有team01项目下的查询、新增、修改或删除的权限,无其他操作权限。
Application创建操作
- 执行以下命令,查看项目管理员team01-admin拥有Project team01的资源权限。
- 可引用的Repositories:
- 全局的
Repositories:https://code.aliyun.com/bigteam/echo-server01.git。 - 项目内的
Scoped Repositories:https://code.aliyun.com/team01/echo-server.git。
- 全局的
- 可引用的Clusters:
https://47.111.XX.XX:6443。
argocd proj get team01 Name: team01 Description: Destinations: https://47.111.XX.XX:6443,* Repositories: https://code.aliyun.com/bigteam/echo-server01.git Scoped Repositories: https://code.aliyun.com/team01/echo-server.git Allowed Cluster Resources: <none> Scoped Clusters: <none> Denied Namespaced Resources: <none> Signature keys: <none> Orphaned Resources: disabled - 可引用的Repositories:
- 执行以下命令,在Project team01之外创建Application。
预期输出:argocd app create team01-admin-echo-server --repo https://code.aliyun.com/bigteam/echo-server01.git --dest-namespace team01-admin-echo-server --dest-server https://47.111.XX.XX:6443FATA[0001] rpc error: code = PermissionDenied desc = permission denied: applications, create, default/team01-admin-echo-server, sub: team01-admin, iat: 2022-10-20T03:20:47Z预期输出表明,在Project team01之外,Application创建失败。
- 执行以下命令,使用未被授权的Repositories和Cluster创建Application。
预期输出:argocd app create team01-admin-echo-server --project team01 --repo https://code.aliyun.com/bigteam/echo-server02.git --path manifests/directory/production --dest-namespace team01-admin-echo-server --dest-server https://47.97.XX.XX:6443FATA[0002] rpc error: code = InvalidArgument desc = application spec for team01-admin-echo-server is invalid: InvalidSpecError: application repo https://code.aliyun.com/bigteam/echo-server02.git is not permitted in project 'team01';InvalidSpecError: application destination {https://xx.xx.xx.xx:6443 team01-admin-echo-server} is not permitted in project 'team01预期输出表明,使用未授权的Reporsitories和Cluster创建Application失败。
- 执行以下命令,在Project team01内,使用允许的Repositories和Cluster创建Application。
预期输出:argocd app create team01-admin-echo-server --project team01 --repo https://code.aliyun.com/bigteam/echo-server01.git --path manifests/directory/production --dest-namespace team01-admin-echo-server --dest-server https://47.111.XX.XX:6443 application 'team01-admin-echo-server' createdapplication 'team01-admin-echo-server' created预期输出表明,在Project team01内部Application创建成功。
该文章对您有帮助吗?