使用 EBS 实验室前,需要在 RAM 控制台创建指定的 RAM 角色和权限策略,授权 EBS 实验室服务访问您的云资源。
前提条件
背景信息
EBS 实验室是块存储(EBS)提供的交互式学习环境,帮助您快速上手云盘、快照等块存储功能。实验室在执行实验任务时,需要调用 ECS、VPC、OSS 等多个云服务的 API,因此需要您提前授权。
授权流程包含以下步骤:
步骤 | 说明 |
创建权限策略 | 创建名为 |
创建 RAM 角色 | 创建名为 |
角色授权 | 将权限策略绑定到 RAM 角色。 |
步骤一:创建权限策略
登录 RAM 控制台。
在左侧导航栏,选择。
单击创建权限策略。
单击脚本编辑页签,将以下策略内容复制到编辑框中,然后单击确定。
策略内容说明,请参见权限说明。
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "fc:GetService", "fc:CreateService", "fc:GetFunction", "fc:CreateFunction", "fc:DeleteFunction", "fc:InvokeFunction", "fc:DeleteService" ], "Resource": "*" }, { "Action": [ "ecs:DescribeDisks", "ecs:CreateDisk", "ecs:AttachDisk", "ecs:ReInitDisk", "ecs:DetachDisk", "ecs:DescribeDisks", "ecs:ReplaceSystemDisk", "ecs:DeleteDisk", "ecs:ResizeDisk", "ecs:ModifyDiskSpec", "ecs:ModifyDiskAttribute", "ecs:DescribeDedicatedBlockStorageClusters", "ecs:DescribeDedicatedBlockStorageClusterDisks", "ecs:CreateDedicatedBlockStorageCluster", "ecs:TagResources", "ecs:UntagResources", "ecs:ListTagResources", "ecs:DescribeImageSupportInstanceTypes", "ecs:DescribeImages", "ecs:DescribeSecurityGroups", "ecs:CreateSecurityGroup", "ecs:DeleteSecurityGroup", "ecs:CreateSnapshot", "ecs:DeleteSnapshot", "ecs:DescribeSnapshots", "ecs:CopySnapshot", "ecs:DescribeAutoSnapshotPolicy", "ecs:DescribeAutoSnapshotPolicyEx", "ecs:ApplyAutoSnapshotPolicy", "ecs:CancelAutoSnapshotPolicy", "ecs:CreateAutoSnapshotPolicy", "ecs:DeleteAutoSnapshotPolicy", "ecs:ModifyAutoSnapshotPolicy", "ecs:ModifyAutoSnapshotPolicyEx", "ecs:RunCommand", "ecs:CreateCommand", "ecs:DeleteCommand", "ecs:InvokeCommand", "ecs:ModifyCommand", "ecs:DescribeCommands", "ecs:DescribeSecurityGroupAttribute", "ecs:DescribeSecurityGroupReferences", "ecs:AuthorizeSecurityGroup", "ecs:AuthorizeSecurityGroupEgress", "ecs:JoinSecurityGroup", "ecs:LeaveSecurityGroup", "ecs:ModifySecurityGroupAttribute", "ecs:DescribeInstances", "ecs:RunInstances", "ecs:CreateInstance", "ecs:StartInstance", "ecs:StopInstance", "ecs:DeleteInstance", "ecs:DeleteInstances", "ecs:ModifyInstanceAttribute", "ecs:AllocatePublicIpAddress", "ecs:StopInvocation", "ecs:DescribeCloudAssistantStatus", "ecs:Createimage", "actiontrail:CreateServiceTrail", "actiontrail:DeleteServiceTrail", "actiontrail:ListServiceTrail" ], "Resource": "*", "Effect": "Allow" }, { "Effect": "Allow", "Action": [ "vpc:ListEnhanhcedNatGatewayAvailableZones", "vpc:CreateVpc", "vpc:DescribeVpcs", "vpc:DescribeVSwitches", "vpc:CreateVSwitch", "vpc:DeleteVpc", "vpc:DeleteVSwitch" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "oss:ListBuckets", "oss:ListObjects" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "cs:CreateCluster", "cs:DescribeKubernetesVersionMetadata", "cs:DescribeClusterDetail", "cs:DeleteCluster", "cs:GetUserConfig", "cs:ListClusterAddonInstances", "cs:GetClusters", "cs:DescribeEdasClusterToken", "cs:CreateEdasClusterRole", "cs:CreateEdasClusterRoleBinding", "cs:DescribeUserPermission" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ros:GetTemplateParameterConstraints", "ros:GetChangeSet", "ros:GetStack", "ros:GetStackDriftDetectionStatus", "ros:GetStackGroup", "ros:GetStackGroupOperation", "ros:GetStackInstance", "ros:GetStackPolicy", "ros:GetStackResource", "ros:GetTemplate", "ros:GetTemplateEstimateCost", "ros:GetTemplateSummary", "ros:ListStackGroupOperations", "ros:PreviewStack", "ros:ValidateTemplate", "ros:CancelUpdateStack", "ros:ContinueCreateStack", "ros:CreateChangeSet", "ros:CreateStack", "ros:CreateStackGroup", "ros:CreateStackInstances", "ros:CreateTemplate", "ros:DeleteChangeSet", "ros:DeleteStack", "ros:DeleteStackGroup", "ros:DeleteStackInstances", "ros:DeleteTemplate", "ros:DetectStackDrift", "ros:DetectStackGroupDrift", "ros:DetectStackResourceDrift", "ros:ExecuteChangeSet", "ros:GenerateTemplatePolicy", "ros:SetDeletionProtection", "ros:SetStackPolicy", "ros:SetTemplatePermission", "ros:SignalResource", "ros:StopStackGroupOperation", "ros:TagResources", "ros:UntagResources", "ros:UpdateStack", "ros:UpdateStackGroup", "ros:UpdateStackInstances", "ros:UpdateStackTemplateByResources", "ros:UpdateTemplate", "ros:ListChangeSets", "ros:ListStackEvents", "ros:ListStackGroupOperationResults", "ros:ListStackGroups", "ros:ListStackInstances", "ros:ListStackOperationRisks", "ros:ListStackResourceDrifts", "ros:ListStackResources", "ros:ListStacks", "ros:ListTagKeys", "ros:ListTagResources", "ros:ListTagValues", "ros:ListTemplates", "ros:ListTemplateVersions" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ebs:DescribeDiskReplicaGroups", "ebs:DescribeDiskReplicaPairs" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ram:GetRole", "ram:CreateUser", "ram:DeleteUser", "ram:CreateRole", "ram:DeleteRole", "ram:ListPoliciesForRole", "ram:CreatePolicy", "ram:DeletePolicy", "ram:AttachPolicyToRole", "ram:DetachPolicyFromRole", "ram:AttachPolicyToUser", "ram:DetachPolicyFromUser", "ram:GetUser", "ram:ListGroupsForUser", "ram:ListPoliciesForUser", "ram:PassRole", "ram:CreateAccessKey", "ram:DeleteAccessKey" ], "Resource": "*" } ] }输入策略名称
AliyunEbsLabDefaultPolicy,单击确定。
步骤二:创建 RAM 角色
在左侧导航栏,选择。
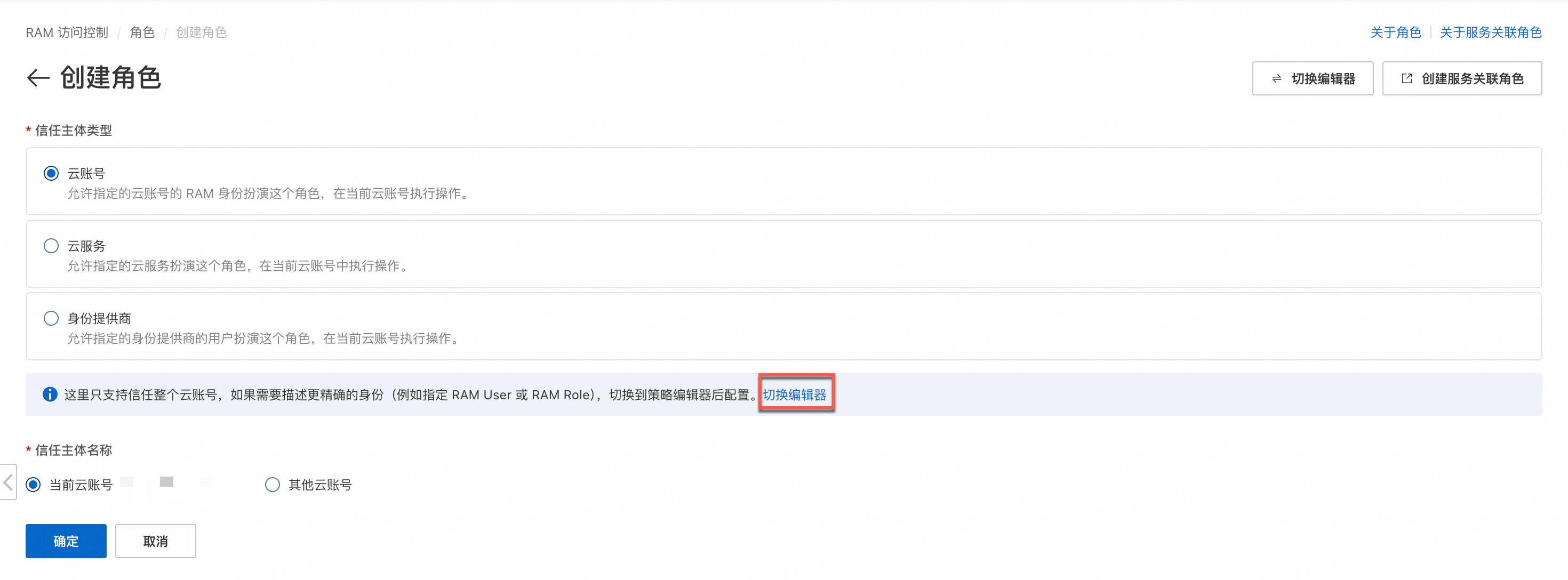
单击创建角色,然后单击切换编辑器。
单击脚本编辑页签,将以下内容复制到编辑框中,然后单击确定。
{ "Version": "1", "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "Service": [ "ebs.aliyuncs.com" ] } } ] }输入角色名称
AliyunEbsLabRole,单击确定。
步骤三:为角色授权
权限说明
AliyunEbsLabDefaultPolicy 策略包含以下服务权限:
服务 | 权限说明 |
函数计算(FC) | 创建、调用、删除服务和函数。 |
云服务器(ECS) | 实例、云盘、快照、安全组、镜像、云助手的完整管理权限。 |
专有网络(VPC) | 创建、查询、删除 VPC 和交换机。 |
对象存储(OSS) | 列出存储空间和对象。 |
容器服务(ACK) | 创建、查询、删除 Kubernetes 集群。 |
资源编排(ROS) | 创建、更新、删除资源栈和模板。 |
块存储(EBS) | 查询云盘复制组和复制对。 |
访问控制(RAM) | 创建、删除用户和角色,管理权限策略。 |
操作审计(ActionTrail) | 创建、删除、查询服务跟踪。 |
